Announcements, Load Balancer, Networking
Manage port forwarding for backend pool with Azure Load Balancer
Posted on
3 min read
Starting today, Azure Load Balancer enables customers to manage port forwarding for Virtual Machine Scale Sets or a group of virtual machines in a backend pool with a single set-up with minimum management overhead.
What is port forwarding?
Port forwarding lets you connect to specific virtual machines by using the Load Balancer frontend IP address and port number. Load Balancer, upon receiving the traffic on a certain frontend port, will forward traffic to the target virtual machine on a specific backend port.
By employing an inbound NAT rule, you can access virtual machines in a virtual network through the IP address and port of the Load Balancer.
Inbound NAT rule or load balancing rule?
In a nutshell, inbound NAT rule is used for traffic forwarding by mapping each virtual machine to a frontend port of the Load Balancer for access. All traffic arriving at the specified frontend port of the Load Balancer will be directly forwarded to a single targeted virtual machine. Therefore, traffic is not load balanced in this case. Inbound NAT rules are useful when you want to forward traffic directly to a specific virtual machine and port combination. While load balancing rules are used to distribute traffic coming to a specific frontend of the Load Balancer across all virtual machines in the backend pool.
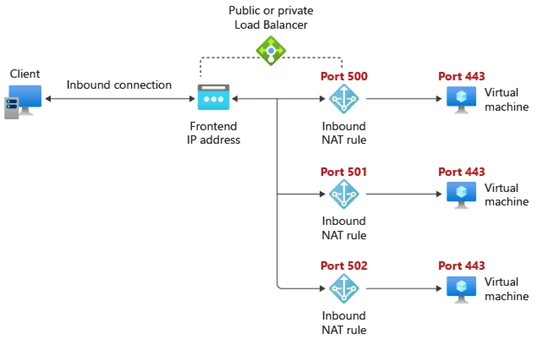
Figure 1: Inbound NAT rule for single machine.
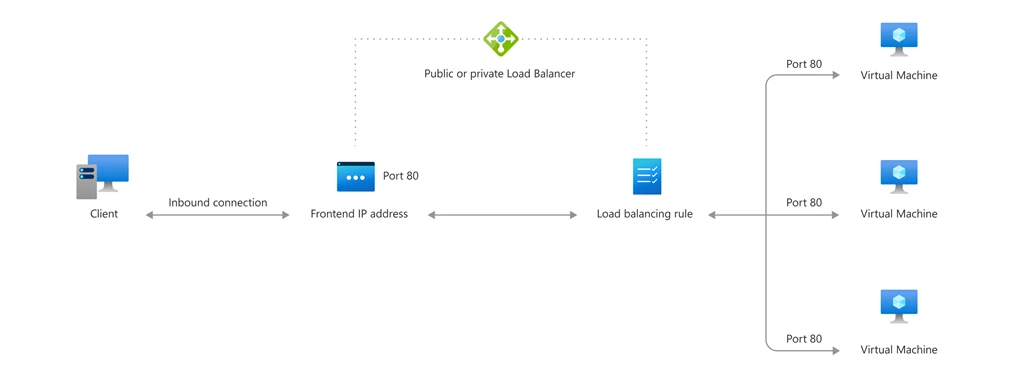
Figure 2: Load Balancing rule.
You can have both load balancing rules and inbound NAT rules on the same Load Balancer. For example, a load balancing rule can be set up for the specific backend pool from frontend port 80 to backend port 80, so that incoming traffic can be distributed across the virtual machines in the backend pool. At the same time, you can also set up an inbound NAT rule for each virtual machine on backend port 443 so that you can use Remote Desktop Protocol (RDP) to access each virtual machine for management purposes.
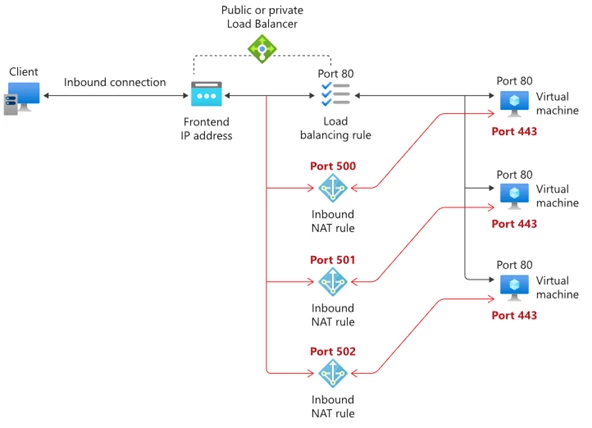
Figure 3: Use both inbound NAT rule and load balancing rule on a backend pool.
What are the customer challenges that we aim to solve?
Inbound NAT rules for individual target machine
When you have a large backend pool with frequent scaling up and down, this approach will create unnecessary overhead. An inbound NAT rule needs to be deleted before the target virtual machine can be taken out of the backend pool. Similarly, whenever scaling up occurs, a new inbound NAT rule for the new virtual machine needs to be created to complete the port forwarding set-up.
Inbound NAT pool
Inbound NAT pool is an existing option for backend pool composed of Virtual Machine Scale Sets. However, updating inbound NAT pool introduces additional steps behind the curtain which could result in longer deployment time. Additionally, this approach is not viable when your backend pool is composed of a group of virtual machines.
Universal port forwarding solution for backend pool of all types
Inbound NAT rule for Virtual Machines Scale Sets, Virtual Machines, or IP addresses in a backend pool
Today, we are announcing the addition of port management for backend pool to inbound NAT rules. It is the preferred solution for setting up port forwarding for backend pool of all types including Virtual Machines Scale Sets, virtual machines, and IP addresses.
Based on frontend port range start, maximum number of machines in backend pool defined for an inbound NAT rule, Load Balancer will pre-allocate a range of frontend ports starting from frontend port range start. The range end is calculated by adding maximum number of machines in the backend pool to frontend port range start to ensure that there are enough frontend ports in the event of scaling up.
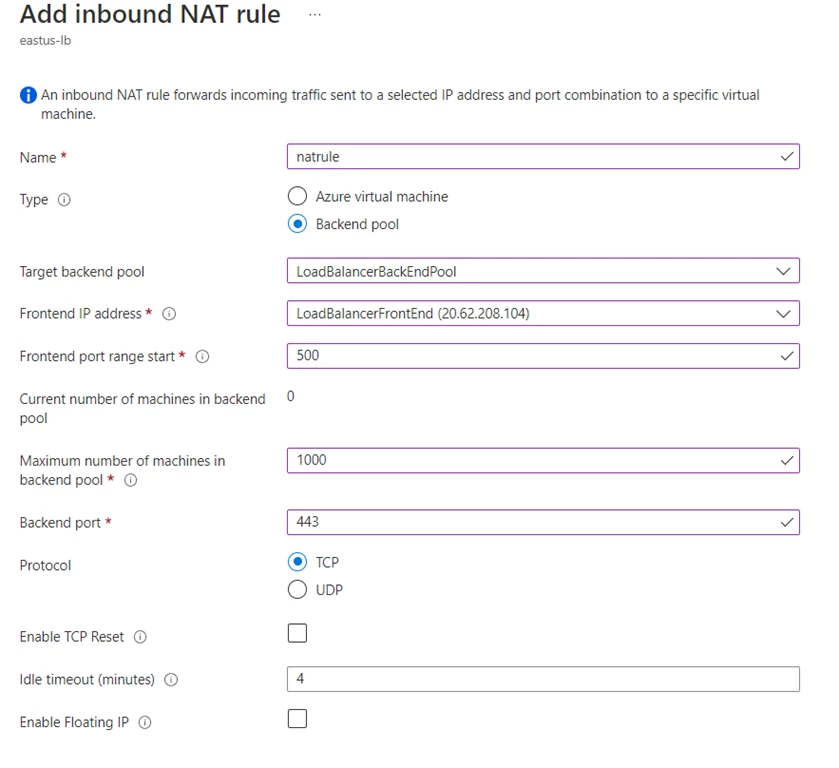
Figure 4: Add inbound NAT rule.
In this example, Load Balancer will pre-allocate 1000 frontend ports starting from port 500. In this case, the backend pool can scale up to 1000 machines without requiring extra management from the customer.
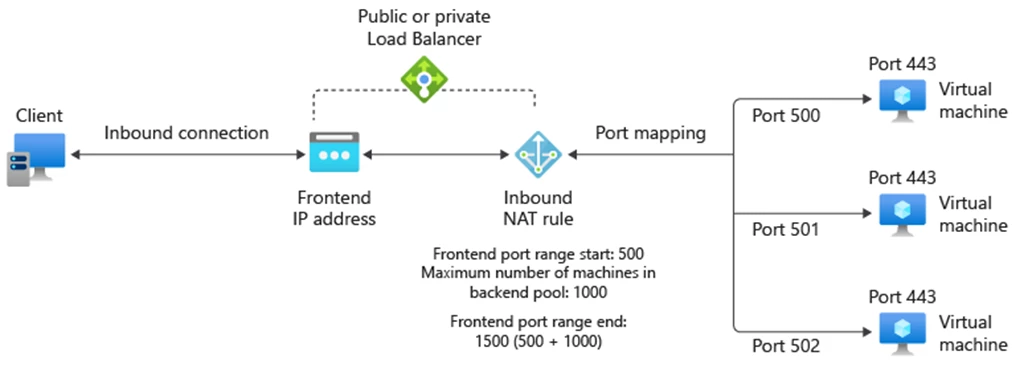
Figure 5: Inbound NAT rule for backend pool.
Retrieve port mapping for individual machines
Once the inbound NAT rule is created, Load Balancer will assign the frontend port to each virtual machine in the backend pool. Port mappings of existing machines will not change in the event of scaling up or down. In this example, to access centralus-vm1 on port 443, you can use https://40.89.253.167:502.
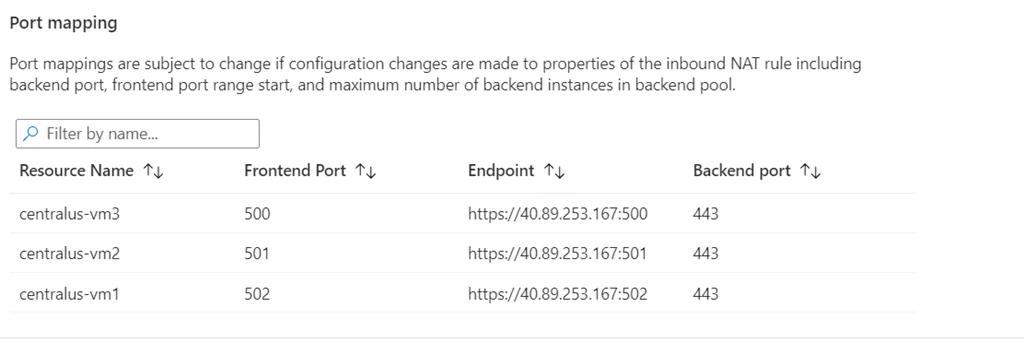
Figure 6: Port mapping for individual machines.