Azure Front Door, Networking, Security, Web Application Firewall
Web application firewall at Azure Front Door service
Posted on
3 min read
You have a great web application, and users from all over the world love it. Well, so do malicious attackers. Cyber-attacks grow each year in frequency and sophistication, and being unprotected against them exposes you to the risks of service interruptions, data loss, and tarnished reputation.
We have heard from many of you that security is a top priority when moving web applications onto the cloud. Today, we are very excited to announce our public preview of the Web Application Firewall (WAF) for the Azure Front Door service. By combining the global application and content delivery network with natively integrated WAF engine, we now offer a highly available platform helping you deliver your web applications to the world, secure and fast!
WAF with Front Door service leverages the scale of and the deep security investments we have made at the Azure edge, and it is designed to protect you from multiple attack vectors such as injection type attacks and volumetric DoS attacks. It inspects each incoming request at Azure’s network edge, stops unwanted traffic before they enter your backend servers, and offers protection at scale without sacrificing on performance. With WAF for Front Door, you have the option to fine tune access to your web application using custom rules that you define, as well as to enable a collection of security rules against common web application vulnerabilities packaged as Managed Rulesets. Furthermore, when you use WAF at Front Door, your security policy management is centralized and any changes you make are instantaneously propagated to all the Front Door edges.
A WAF policy is the building unit of WAF which defines the security posture for your web application. It can have two types of security rules: custom rules and a set of pre-configured rule groups known as a Managed Ruleset. Azure managed Default Rule Set is updated by Azure as needed to adapt to new attack signatures. If you have a cloud native, Internet-facing web application such as a web app hosted on Azure PaaS platform it is very simple to add Front Door with default WAF policy. Just a few clicks away, your web application is protected from common OWASP TOP 10 exploitations and with latency optimization offered by Front Door service.
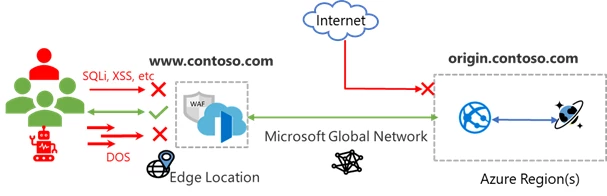
Figure 1 Protecting your Web App with WAF at Front Door
If you are like many of our customers who have compliance and BCDR requirements for your business-critical applications, you probably have your web applications hosted in multiple regions. WAF with Front Door offers centralized policy management and global load balancing supporting many routing options to your backends.
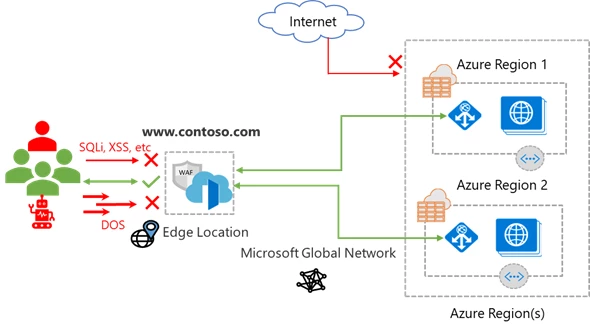
Figure 2 Protecting your multi-region web application with WAF at Front Door
WAF with Front Door can protect backends hosted on Azure as well as these that are hosted on other clouds or on Premise. You may further lock down your backends to allow only traffic from Front Door and deny direct access from the Internet. WAF at Front Door allows granular access and rate control via custom rules. You may create custom rules along the following dimensions:
- IP allow list and block list: control access to your web applications based on list of client IP addresses or IP address ranges. Both IPv4 and IPv6 are supported.
- Geographic based access control: control access to your web applications based on a client’s country code.
- HTTP parameters-based access control: control access to your web applications based on string matching of HTTP(S) request parameters such as query string, post args, request Uri, request header, and request body.
- Request method-based access control: control access to your web applications based on HTTP request method such as Get, Put, and Head.
- Size constraint: control access to your web applications based on the lengths of specific parts of a request such as query string, Uri, or request body.
- Rate limiting rules: A rate control rule is to limit abnormal high traffic from any client IP. You may set a threshold on number of web requests allowed by a client IP during a one-minute duration. Rate can be combined with match conditions, for example, rate limit access to a specific Uri path.
WAF charges based on the number of WAF policies and rules you create, types of managed rule set you choose, and the number of web requests that you receive. During public preview, WAF at Front Door is free of charge.
As we continue to enhance Azure WAF offering, would love to hear your feedback. You can try Web Application Firewall with Front Door today using portal, ARM templates, or PowerShell. For more information, visit the detailed documentation for Web Application Firewall (WAF) for the Azure Front Door service.