Last September at Ignite we announced plans for better web application security by adding Web Application Firewall to our layer 7 Azure Application Gateway service. We are now announcing the General Availability of Web Application Firewall in all Azure public regions.
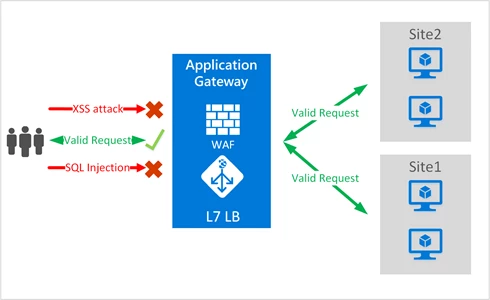
Web applications are increasingly targets of malicious attacks that exploit common known vulnerabilities, such as SQL injection and cross site scripting attacks. Preventing such exploits in the application requires rigorous maintenance, patching, and monitoring at multiple layers of the application topology. A centralized web application firewall (WAF) protects against web attacks and simplifies security management without requiring any application changes. Application and compliance administrators get better assurance against threats and intrusions.
Azure Application Gateway is our Application Delivery Controller (ADC) layer 7 network service offering capabilities including SSL termination, true round robin load distribution, cookie-based session affinity, multi-site hosting, and URL path based routing. Application Gateway provides SSL policy control and end to end SSL encryption to provide better application security hardening. These capabilities allow backend applications to focus on core business logic while leaving costly encryption/decryption, SSL policy, and load distribution to the Application Gateway. Web Application Firewall integrated with Application Gateway’s core offerings further strengthens the security portfolio and posture of applications protecting them from many of the most common web vulnerabilities, as identified by Open Web Application Security Project (OWASP) top 10 vulnerabilities. Application Gateway WAF comes pre-configured with OWASP ModSecurity Core Rule Set (3.0 or 2.2.9), which provides baseline security against many of these vulnerabilities. With simple configuration and management, Application Gateway WAF provides rich logging capabilities and selective rule enablement.
Benefits
Following are the core benefits that Web Application Firewall provides:
Protection
- Protect your application from web vulnerabilities and attacks without modifying backend code. WAF addresses various attack categories including:
- SQL injection
- Cross site scripting
- Common attacks such as command injection, HTTP request smuggling, HTTP response splitting, and remote file inclusion attack
- HTTP protocol violations
- HTTP protocol anomalies
- Bots, crawlers, and scanners
- Common application misconfigurations (e.g. Apache, IIS, etc.)
- HTTP Denial of Service
- Protect multiple web applications simultaneously. Application Gateway supports hosting up to 20 websites behind a single gateway that can all be protected against web attacks.
Ease of use
- Application Gateway WAF is simple to configure, deploy, and manage via the Azure Portal and REST APIs. PowerShell and CLI will soon be available.
- Administrators can centrally manage WAF rules.
- Existing Application Gateways can be simply upgraded to include WAF. WAF retains all standard Application Gateway features in addition to Web Application Firewall.
Monitoring
- Application Gateway WAF provides the ability to monitor web applications against attacks using a real-time WAF log that is integrated with Azure Monitor to track WAF alerts and easily monitor trends. The JSON formatted log goes directly to the customer’s storage account. Customers have full control over these logs and can apply their own retention policies. Customers can also ingest these logs into their own analytics system. WAF logs are also integrated with Operations Management Suite (OMS) so customers can use OMS log analytics to execute sophisticated fine grained queries.
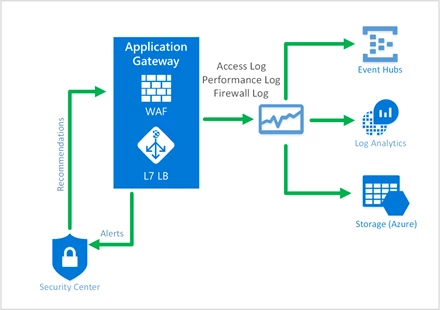
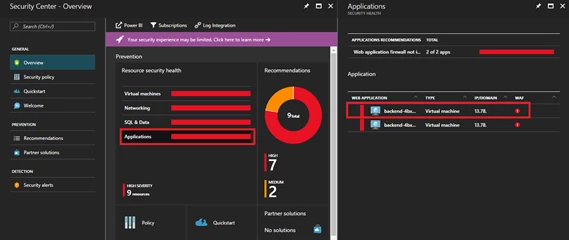
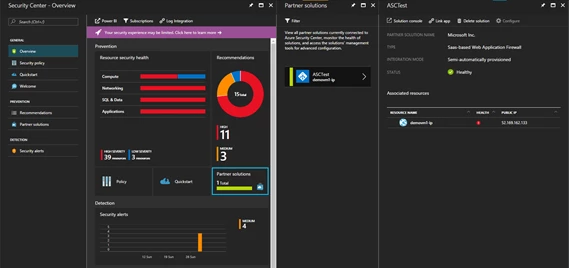
- Application Gateway WAF will shortly be integrated with Azure Security Center to provide a centralized security view of all your Azure resources. Azure Security Center scans your subscriptions for vulnerabilities and recommends mitigation steps for detected issues. One such vulnerability is the presence of web applications that are not protected by a WAF.
Customization
- Application Gateway WAF can be run in detection or prevention mode. A common use case is for administrators to run in detection mode to observe traffic for malicious patterns. Once potential exploits are detected, turning to prevention mode blocks suspicious incoming traffic.
- Customers can customize WAF RuleGroups to enable/disable broad categories or sub-categories of attacks. Therefore, an administrator can enable or disable RuleGroups for SQL Injection or Cross Site Scripting (XSS). Customers can also enable/disable specific rules within a RuleGroup. For example, the Protocol Anomaly RuleGroup is a collection of many rules that can be selectively enabled/disabled.
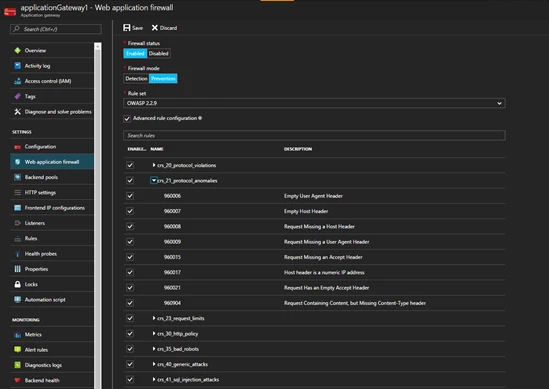
Embracing Open Source
Application Gateway WAF uses one of the most popular WAF deployments – OWASP ModSecurity Core Rule Set to protect against the most common web vulnerabilities. These rules, which conform to rigorous standards, are managed and maintained by the open source community. Customers can choose between rule set CRS 2.2.9 and CRS 3.0. Since CRS 3.0 offers a dramatic reduction in false positives, we recommend using CRS 3.0.
Summary and next steps
General availability of Web Application Firewall is an important milestone in our Application Gateway ADC security offering. We will continue to enhance the WAF feature set based on your feedback. You can try Application Gateway Web Application Firewall today using portal or ARM templates. Further information and detailed documentation links are provided below.
- Application Gateway WAF pricing
- More technical details on Application Gateway WAF
- A comprehensive list of WAF rule schemas and RuleGroup/Rules
- Step by step guide to create and customize
- Deployment by an ARM template
- ARM API
- PowerShell and CLI support will be available soon
