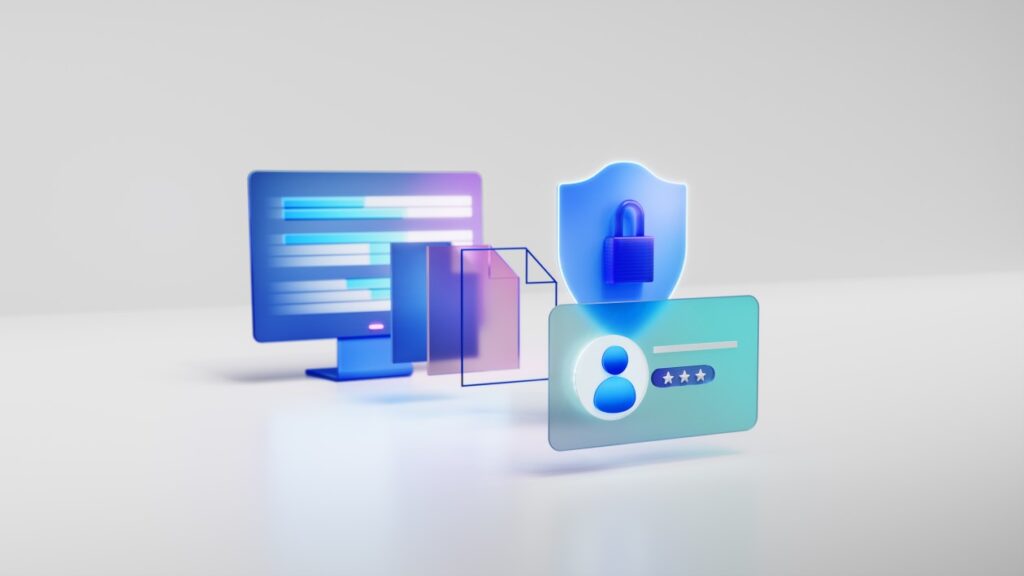
Azure IaaS: Defense in depth built on secure-by-design principles
Security for cloud infrastructure is no longer defined by a single control, product, or boundary. Modern threats target identity, software supply chains, control planes, networks, and data simultaneously.