Azure Blob Storage, Databases, Storage
Announcing Virtual Network integration for Azure Storage and Azure SQL
Posted on
2 min read
Today, we are glad to announce the public preview of Virtual Network (VNet) Service Endpoints for Azure Storage and Azure SQL.
For many of our customers moving their business-critical data to the cloud, data breaches remain a top concern. Various Azure services that store or process the business data have Internet-reachable IP addresses. Leaked credentials or malicious insiders with administrative privileges gaining access to the data, from anywhere in the world, is an increasing concern to our customers.
To protect against these threats, private connectivity to Azure services is becoming essential to moving more critical workloads to the cloud. Most customers want to limit access to their critical resources to only their private environments, i.e. their Azure Virtual Networks and on-premises.
While some of the Azure services can be directly deployed into VNets, many others still remain public. With VNet service endpoints, we are expanding Virtual Network support to more multi-tenant Azure services.
Service endpoints extend your VNet private address space and identity to the Azure services, over a direct connection. This allows you to secure your critical service resources to only your virtual networks, providing private connectivity to these resources and fully removing Internet access.
Configuring service endpoints is very simple with a single click on a subnet in your VNet. Direct route to the services is auto-configured for you. There are no NAT or gateway devices required to set up the endpoints. You also no longer need reserved, public IP addresses in your VNets to secure Azure resources through IP firewall. Service endpoints makes it easy to configure and maintain network security for your critical resources.
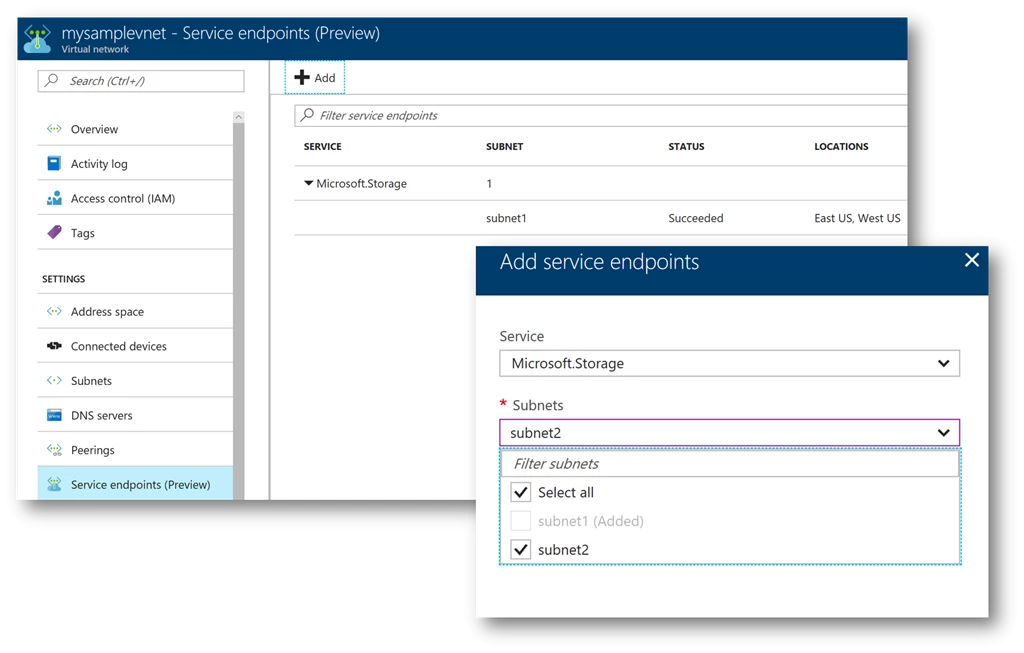
Step1: Set up service endpoints once on your Virtual Network. Network administrators can turn this setting independently, allowing for separation of duties.
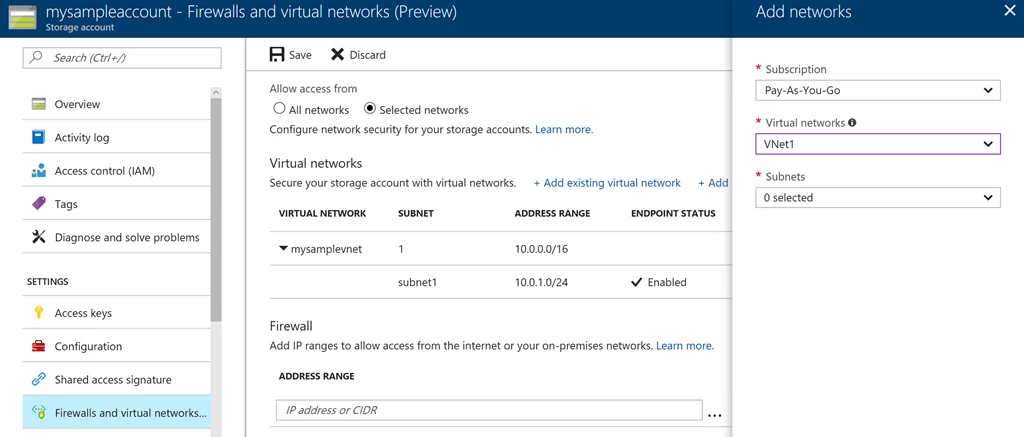
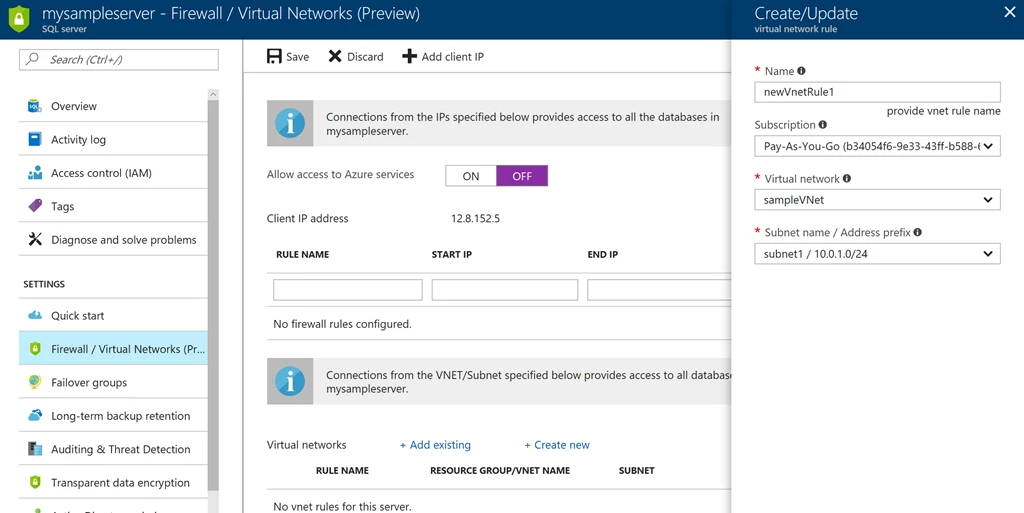
Step 2: Secure your new or existing Azure service resources to the VNet, with a simple click. Set up once for the Storage account or SQL server and automatically applies to any access to child resources. Data administrators can set up independently (optional).
Service endpoints is available in preview for below services and regions:
Azure Storage: WestUS, EastUS, WestCentralUS, WestUS2, AustraliaEast, and AustraliaSouthEast
Azure SQL: EastUS, WestCentralUS, WestUS2
We will be expanding the feature to more regions soon.
We are very excited to bring enhanced network security for your Azure service resources. This is only a beginning for our roadmap for tightening security for Azure services. We will expand the service endpoints to more Azure services. In addition to service endpoints, we are also very committed to giving you private connectivity to your Azure resources, from your firewalls and on-premises. Service tags is yet another investment in this direction, for your Network Security Groups (NSGs) to selectively open access only to Azure services from your VNets. Service tags is also available in preview now. More enhancements to follow!
Next Steps
To start using VNet Service Endpoints, refer to the documentation.
For full list of network security capabilities in Azure, see “Azure Network security”.
We need your help in improving the features and broadening network security for Azure services. Share your feedback on StackOverflow with the tag “vnet-azure-services”. You can also email us directly at vnetserviceintegration@microsoft.com
For those of you at Microsoft Ignite, we will be covering the feature in more detail in our session on security: “Network security for applications in Azure”! See you all there!